Faultry is an innovative website audit tool designed to put your site through a rigorous "car crash test" before launch or for ongoing maintenance. It goes beyond traditional performance checks to audit critical aspects like mobile responsiveness, social media card previews, security headers, and AI discoverability, ensuring your website is robust and ready for the modern web.
This SaaS is ideal for web developers, site owners, and marketing professionals who need to ensure their online presence is flawless, secure, and easily discoverable by both users and AI crawlers.
Key Features
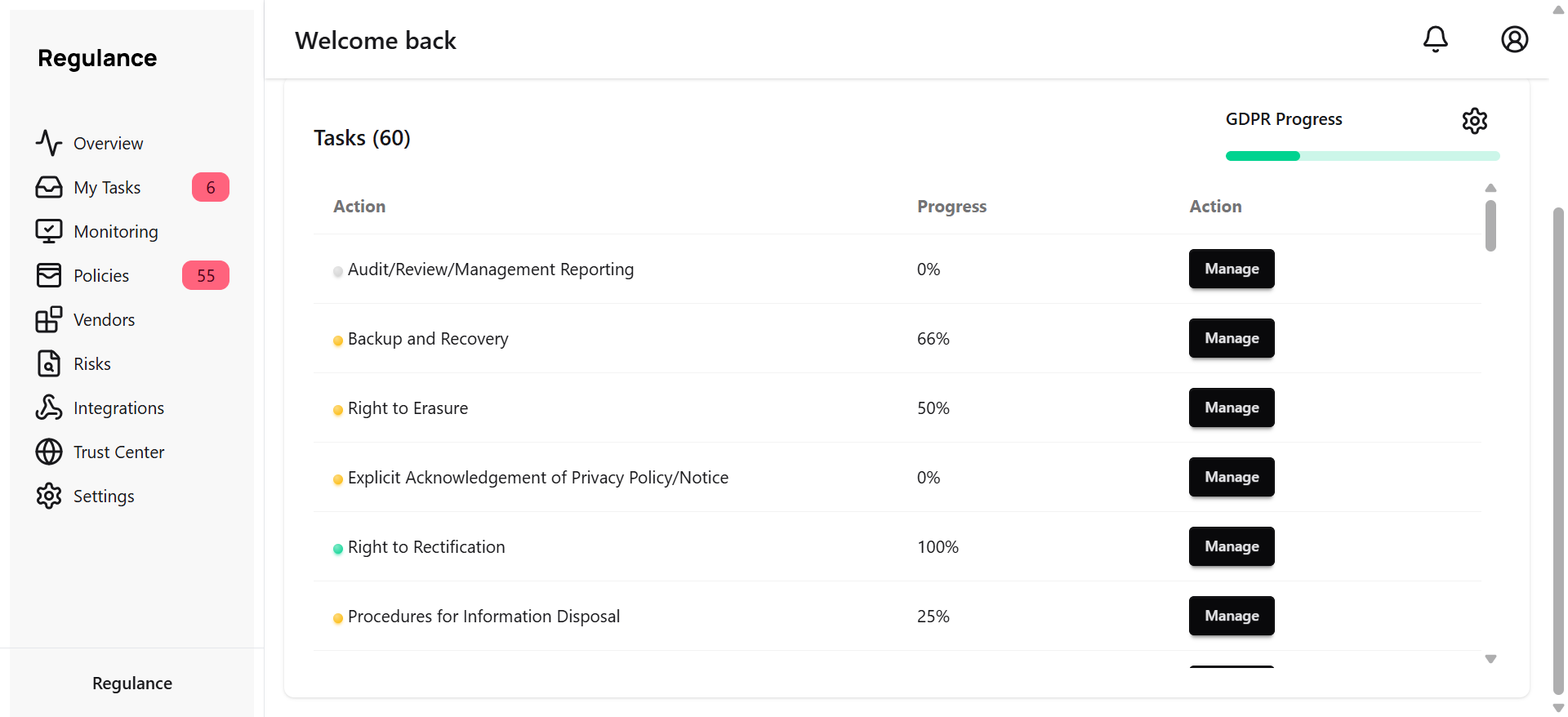
Comprehensive 6-Point Audit: Deep checks on security, mobile viewport, social cards, AI visibility, console errors, and performance (Core Web Vitals).
Stack-Specific Fixes: Generates copy-paste code snippets tailored for popular frameworks like Next.js, React, SvelteKit, Nuxt, Vue, and Express.
Real-World Mobile Rendering: Verifies actual mobile viewport behavior, including horizontal overflow, touch targets, and font zoom risks, not just a responsive design checkbox.
Social Card Previews: Shows exactly how your links will appear when shared on platforms like Twitter, LinkedIn, Discord, and Slack.
AI Discoverability Checks: Audits llms.txt, robots.txt, sitemap accessibility, and detects cloaking to ensure AI crawlers can find and understand your content.
Advanced Security Header Analysis: Goes beyond mere presence to check the effectiveness of HSTS, CSP, X-Frame-Options, DNSSEC, CAA, and Mixed Content.
Use Cases
Faultry is an indispensable tool for ensuring a smooth website launch. Developers can leverage its deep checks to identify and rectify critical issues such as security vulnerabilities, mobile display glitches, or broken social sharing previews before their site goes live, preventing potential user frustration and reputational damage.
For established websites, Faultry serves as a powerful ongoing optimization and maintenance solution. Site owners can regularly audit their platforms to maintain peak performance, bolster security, and enhance AI visibility, ensuring their content remains discoverable and provides an optimal user experience. It's also excellent for quickly troubleshooting common problems like console errors, performance bottlenecks, or inaccurate social media link previews, providing actionable insights and direct fixes.
Pricing Information
Faultry operates on a freemium model. Your first comprehensive audit is completely free, requiring no signup, and provides a full letter grade along with detailed results for all six checks. Access to stack-specific fix code is available through the Developer Fix Kit, suggesting a paid tier for advanced remediation tools.
User Experience and Support
The platform is designed for ease of use: simply paste your URL into the terminal to initiate an audit. The process is quick, with most audits completing in under 15 seconds. Results are presented as an AI assessment, offering clear insights and actionable recommendations. All audit reports are private by default, accessible via a secure magic link, ensuring data confidentiality. Users can flag specific reports for admin review if needed, and the Developer Fix Kit provides ready-to-use code snippets for immediate implementation.
Technical Details
Faultry performs a multi-layered analysis, including HTTP checks for security headers (HSTS, CSP, DNSSEC) and browser-based rendering for mobile and console errors. It specifically examines Open Graph (OG) tags for social media previews and AI-specific files like llms.txt and robots.txt. Performance metrics include Core Web Vitals such as LCP, CLS, TTFB, FCP, Speed Index, and TBT. The platform intelligently auto-detects your site's tech stack to generate tailored fixes for frameworks including Next.js, React, SvelteKit, Nuxt, Vue, and Express.
Pros and Cons
Pros:
More comprehensive than Lighthouse, covering crucial areas like security, social cards, and AI visibility.
Provides stack-specific, copy-paste code fixes, significantly speeding up remediation.
Offers a free initial audit without requiring signup, making it accessible for quick checks.
Ensures data privacy with reports being private by default.
Fast audit completion, delivering results in under 15 seconds.
Focuses on real-world issues and actionable insights for launch readiness.
Cons:
The Developer Fix Kit, containing stack-specific code, is likely a paid feature, which isn't explicitly stated as free.
While reports can be flagged for admin review, direct customer support channels aren't detailed.
Implementing some advanced fixes might still require developer expertise, despite provided code snippets.
Conclusion
Faultry stands out as an essential "car crash test" for any website, offering unparalleled depth in auditing critical aspects often overlooked by standard tools. By providing actionable, stack-specific fixes and focusing on real-world performance, security, and discoverability, it empowers developers and site owners to launch and maintain truly robust online experiences. Explore Faultry today to ensure your website doesn't just launch, but thrives.